Protect our Internet rights now!
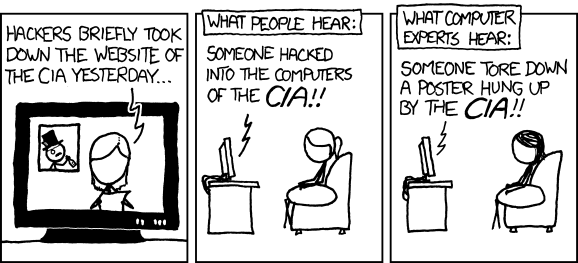
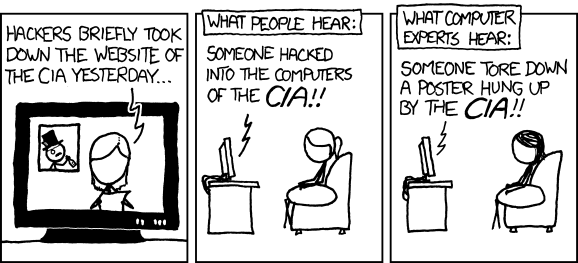
Again, not really that impressive... I'm not saying they *can't* do really impressive things, I'm saying what most people think of as "hacking" (like what they're doing right now, defacing websites, etc) is the most basic AND easy shit. They do it because it's quick and draws attention.
this is what I'm saying

Now, this shit was much more impressive:
http://arstechnica.com/tech-policy/n...bgary-hack.ars
Read that whole thing and you'll get what I'm talking about.
this is what I'm saying

Now, this shit was much more impressive:
http://arstechnica.com/tech-policy/n...bgary-hack.ars
Read that whole thing and you'll get what I'm talking about.
I am not trying to talk down to you ... just understand that the CIA's *front page website* isn't much more secure than s2ki's front page.. or any other website. Possibly less so. The actual data that the CIA has, the actual fundamentals of their systems... that shit is stored on entirely different servers with entirely different security. Getting even the tiniest bit of info out of a secure network is 10000000x harder than getting onto someone's public facing website. It's just like the comic... it's spraypainting their front door versus breaking into their actual building. Ballsy - but not difficult.
Also - side note - sql injection is generally prevented on the application development side, not the DBA's responsibility necessarily. If he/she's at all involved in the process, then sure, that should be addressed... but if someone else is writing the app and the stored procedures and such...

Thread
Thread Starter
Forum
Replies
Last Post
energetic
Γενικά Θέματα εκτός S2000
1
Jan 19, 2010 12:42 AM









